This is an old revision of the document!
Table of Contents
Block Cipher Modes
Abstract
Block cipher is one of the most widely-used tool in cryptography, and its mode of operation features the use of a symmetric-key block-cipher algorithm in providing information security such as confidentiality or authenticity. Five modes of operation with AES algorithm will be discussed in this paper: Electronic Codebook (ECB), Cipher Block Chaining (CBC), Cipher Feedback (CFB), Output Feedback (OFB), and Counter (CTR). These modes can provide cryptographic protection for sensitive, but classified, computer data.
Keywords: Computer security; cryptography; block cipher; mode of operation
Introduction
Block cipher is one of the most widely-used tool in cryptography, but itself is only used of one fixed-length group of bits called a block [1]. A mode of operation describes how to repeatedly apply a cipher's single-block operation to securely transform amounts of data larger than a block [2].
The five modes—the Electronic Codebook (ECB), Cipher Block Chaining (CBC), Cipher Feedback (CFB), Output Feedback (OFB), and Counter (CTR) modes can provide data confidentiality.
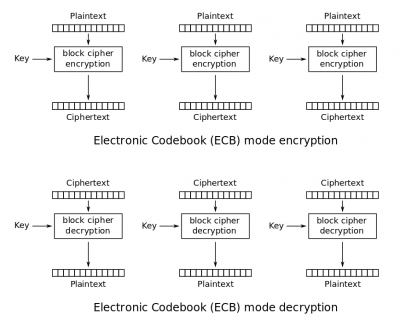
Electronic Codebook (ECB)
The electronic codebook (ECB) is the simplest encryption mode, which is named after conventional physical codebooks. For the given key, ECB features the same assignment of a fixed ciphertext block to each plaintext. Each block is been manipulated separately.
In ECB encryption and ECB decryption, multiple forward cipher functions and inverse cipher functions can be computed in parallel under a given key.
The ECB mode has an disadvantages—a lack of diffusion, under a given key, any given plaintext block always gets encrypted to the same cyphertext if they are identical.